Whether you’re a fleet manager or an individual looking for the best vehicle management platform, GLUON is the right platform designed with modern automotive needs […]
Blogs
How to Choose the Right POS System for Your Business
Selecting the perfect Point of Sale (POS) system for your business is no small task. Whether you run a retail store, a restaurant, or any […]
Buy Kat Walk Mini, a High-End Omni-Directional Treadmill, for a Thrilling VR Experience
Designed and advertised by KATVR, Kat Walk Mini is the latest omni-directional treadmill that allows you to enjoy a full 360 VR experience you can’t […]
Tips for Using DALL-E 2 and Mastering Image Generation
OpenAI’s DALL-E 2 is one of the most impressive AI tools available today for generating realistic images from text. However, to truly unlock its full […]
Digital, Offset and Large Format Printing in Los Angeles from Axiom Designs
Axiom Designs print shop is very popular in the market of printing services, offering our customers the best conditions for cooperation. Digital printing, offset printing […]
Best Alternative Dating Apps to Tinder
Are you looking for the latest dating apps that can provide you with more features? You’re at the right place. Finding your soul mate can […]
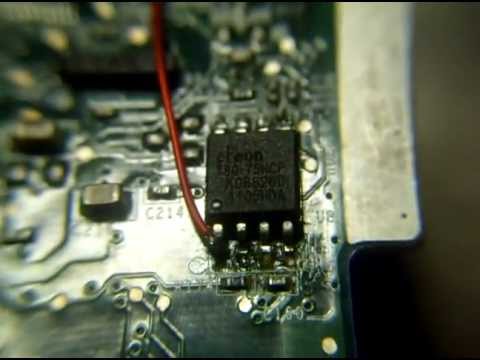
Replacement of BIOS chip – Updating System BIOS
Motherboards of this time have mostly EEPROM BIOS chip that are able to reprogram. These chips are also known as flash ROM or PROM, flashing […]
Great Functions Of Dell Laptops
Dell laptop computers have most definitely established the market on fire. This results from the advanced as well as advancement technology most customers see on […]
Demand for IT Cyber SECURITY Professionals in 2017
A certified ethical hacker is a talented professional who knows and understands how to observe vulnerabilities and weaknesses in target systems and utilises these tools […]
STRIDE Threat Modeling — Why Is it Necessary?
STRIDE Threat Modeling is a process that can be used to identify security risks in systems and software. The acronym STRIDE stands for Spoofing, Tampering, […]